| FindBook |
有 1 項符合
Recovering From Identity Theft的圖書 |
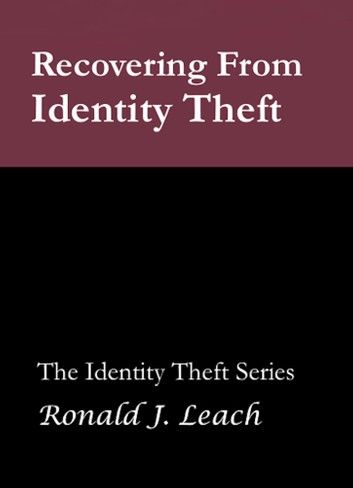 |
Recovering From Identity Theft 作者:Ronald J. Leach 出版社:AfterMath 出版日期:2013-12-28 語言:英文 |
| 圖書館借閱 |
| 國家圖書館 | 全國圖書書目資訊網 | 國立公共資訊圖書館 | 電子書服務平台 | MetaCat 跨館整合查詢 |
| 臺北市立圖書館 | 新北市立圖書館 | 基隆市公共圖書館 | 桃園市立圖書館 | 新竹縣公共圖書館 |
| 苗栗縣立圖書館 | 臺中市立圖書館 | 彰化縣公共圖書館 | 南投縣文化局 | 雲林縣公共圖書館 |
| 嘉義縣圖書館 | 臺南市立圖書館 | 高雄市立圖書館 | 屏東縣公共圖書館 | 宜蘭縣公共圖書館 |
| 花蓮縣文化局 | 臺東縣文化處 |
|
|
The headline was dreadful from a consumer's perspective. Data from all Target stores had been criminally hacked, and essential information on forty million credit and debit cards was stolen in November and December of 2013. There are reports of angry consumers calling Target's customer service and demanding help. The merchant is the wrong place to call, just as it was pointless to call T. J. Maxx when the data contained on sixty million of their customer's cards were illegally obtained by criminal hackers.
This easy-to-understand, 79-page book is the fourth in the Identity Theft series. It is intended for the general, non-specialist reader, provides a set of overall strategies and specific actions you should take if you are the victim of identity theft.
There are three appendices. The first appendix contains contact information for the Federal Trade Commission, the three major credit reporting agencies, many US banks, many consumer protection organizations, and a few of the more established companies that specialize in identity theft protection and recovery. The second appendix contains a checklist for protecting yourself from identity theft. Appendix three also contains a checklist; this one is used to aid you in recovering from identity theft if you are a victim.
Ron Leach's lectures on identity theft have been attended by more than 3,500 people. Many more have heard him on closed-circuit television. This experience, and his long experience as a professor of computer science make him uniquely qualified to write this book, the fourth in AfterMath’s Identity Theft Series.
About the Author
I recently retired from being a professor of computer science at Howard University for over 25 years, with 9 as a department chair. (I was a math professor for 16 years before that.) While I was department chair, we sent more students to work at Microsoft in the 2004-5 academic year than any other college or university in the United States. We also established a graduate certificate program in computer security, which became the largest certificate program at the university. I had major responsibility for working with technical personnel to keep our department’s hundreds of computers functional and virus-free, while providing email service to several hundred users. We had to withstand constant hacker attacks and we learned how to reduce the vulnerability of our computer systems.
As a scholar/researcher, I studied complex computer systems and their behavior when attacked or faced with heavy, unexpected loads. I wrote five books on computing, from particular programming languages, to the internal structure of sophisticated operating systems, to the development and efficient creation of highly complex applications. My long-term experience with computers (I had my first computer programming course in 1964) has helped me understand the nature of many of the computer attacks by potential identity thieves and, I hope, be able to explain them and how to defend against them, to a general audience of non-specialists.
|